🥷🏻 Infecting cell phones with spyware, hacking video surveillance systems and telecommunications networks, exploiting weaknesses in IoT devices... There are several ways to geolocate people of interest, a growing threat to businesses and governments.
https://www.tarlogic.com/blog/geolocate-people-of-interest/
Cybersecurity experts
Do your headphones allow Bluetooth pairing without you being aware of it? Does your pulse oximetry bracelet have a fixed MAC address that would make it easier to track you in real time?
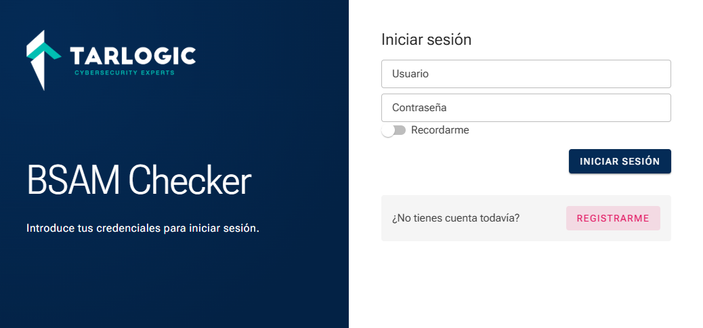
With BSAM Checker, a 100% free, automated tool designed by the Innovation Department at @Tarlogic, you can check whether your IoT devices have security or privacy vulnerabilities related to the Bluetooth standard and notify the manufacturer so they can fix them.
👉🏼 Take a look at the presentations of the research we have done over the last 5 years on Bluetooth security: https://github.com/TarlogicSecurity/Talks
👉🏼 Check the security of your devices using BSAM Checker: https://bsamchecker.tarlogic.com/
La Masía, La Fábrica, A Madroa, Abegondo…
Don’t get too carried away. We’ve got our own academy too.
And they’re coming ready to hack the world. 💻⚡
Alright, come on — we all know each other by now. Time to do what we do best after all that hacking.
See you in a bit for some beers. 🍺
In cybersecurity, every second counts.
At our stand, it does too.
Your mission: Stop the stopwatch exactly at second 10.
Not 9. Not 11.
False positives don’t count here. 🎯
100% free and automatic. That's BSAM Checker, the software designed by the Innovation Department at @Tarlogic, so companies and citizens can audit their Bluetooth devices without knowing anything about it or investing resources.
https://www.tarlogic.com/news/bsam-checker-detecting-vulnerabilities-bluetooth/
🛜 A dongle and a computer. With BSAM Checker, you don't need anything else to check that your IoT devices don't have Bluetooth-related vulnerabilities. @antoniovazquezblanco is already presenting this 100% free program from @Tarlogic at @rootedcon.
Lots of hacking, lots of 0-days… but at 20:00 it’s time to patch the thirst. 🍺
We’ll be waiting for you in the RootedCON networking area for the classic beers with Estrella Galicia.
Because some exploits are better told with a beer in hand.
One more year at RootedCON. T-shirt ready, attitude too.
Because some things are built to be hot... not to be hacked. 🔥
There is an underground economy in which alleged data leaks consisting of obsolete or manipulated information are sold. Alejandro Pachés presented @Tarlogic's research on the Leak-as-a-Service model at @rootedcon.
https://www.tarlogic.com/news/market-for-fake-data-leaks/
Alejandro Julián Pachés' presentation at @rootedcon begins. Our colleague is explaining the key features of a criminal business model in which obsolete, manipulated, or false data leaks are traded, but with the appearance of being real.
Something hot is cooking… You’ll understand it very soon.
See you at RootedCON 2026.
🏆 @Tarlogic is once again featured in the FT-1000 ranking, compiled by Financial Times and @statistacharts which highlights the European companies with the most remarkable growth over the last four years. This recognition highlights the consolidation of our company 👇🏻
https://www.tarlogic.com/news/europes-fastest-growing-companies-ft-1000/
🛜 Want to know if your heart rate monitor or headphones are secure? Miguel Tarascó and @antoniovazquezblanco from the Innovation Department at @Tarlogic will present BSAM Checker at @rootedcon, a free program that automates security audits of Bluetooth devices.
🤥 What if many of the data leaks from companies were fake? Alejandro Julián Pachés, Senior Threat Intelligence Analyst at @Tarlogic will present research on the business of generating fake leaks at @rootedcon.
Are you fully leveraging all the capabilities of your EDR/XDR?
Find out to what extent your Threat Hunting service is maximizing the technology’s potential by deploying an optimal approach to detect and respond to the most sophisticated threats 👇
https://www.tarlogic.com/blog/proactive-threat-hunting-do-you-have-optimal-approach/
🫀 What would happen if a surgical robot stopped working in the middle of an operation? The cybersecurity of medical devices is key to protecting patients. How can security incidents be prevented? 👇🏻
https://www.tarlogic.com/blog/cybersecurity-for-medical-devices/
🎯 Patents, cutting-edge technology, pioneering research... The most advanced cybercriminal groups have set their sights on intellectual property. How can companies defend themselves against highly sophisticated attacks?
https://www.tarlogic.com/blog/intellectual-property-and-cybersecurity/
Not a bad day. Just the Internet.
🥷🏻 Internal security threats pose a major risk to companies and can trigger very serious and costly incidents. How can companies address them technically and organizationally?
https://www.tarlogic.com/blog/internal-security-threats/