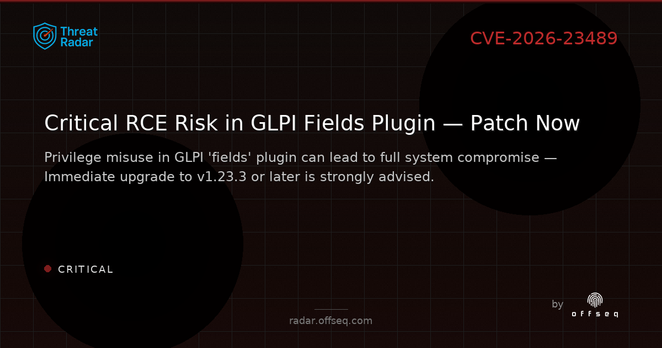
🚨 CVE-2026-23489 (CRITICAL, CVSS 9.1): GLPI 'fields' plugin (<1.23.3) allows privileged users to execute arbitrary PHP code (RCE risk). Patch to 1.23.3+, review permissions, and monitor activity. https://radar.offseq.com/threat/cve-2026-23489-cwe-20-improper-input-validation-in-9483a14f #OffSeq #GLPI #CVE202623489 #infosec
OffSeq is a cybersecurity company enhancing organizational digital resilience through comprehensive protection against evolving cyber threats. We offer specialized services for businesses of all sizes, with particular expertise in Baltic, Scandinavian, Belgian markets and EU regulatory compliance.
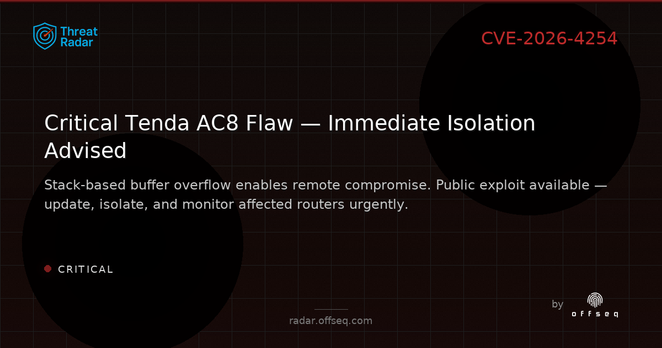
🚨 CRITICAL: CVE-2026-4254 in Tenda AC8 (fw ≤16.03.50.11) enables remote stack buffer overflow via /goform/SysToolChangePwd. Public exploit out — isolate & monitor! No patch yet. https://radar.offseq.com/threat/cve-2026-4254-stack-based-buffer-overflow-in-tenda-501e8b3e #OffSeq #CVE20264254 #RouterSecurity #Vuln
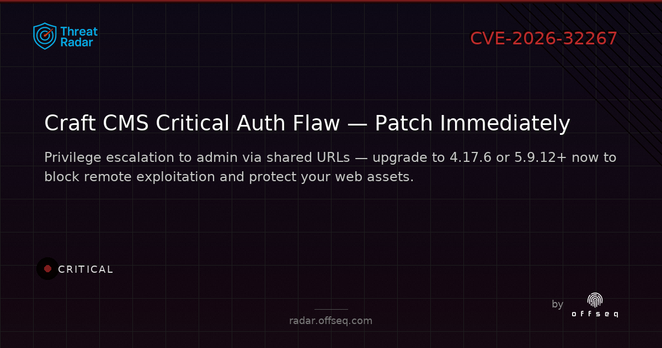
🚨 CRITICAL: CVE-2026-32267 in Craft CMS (4.x <4.17.6, 5.x <5.9.12) — incorrect auth allows privilege escalation to admin via shared URLs. Upgrade ASAP! Details: https://radar.offseq.com/threat/cve-2026-32267-cwe-863-incorrect-authorization-in--65bf3522 #OffSeq #CraftCMS #CVE202632267 #Vulnerability
Chamilo LMS < 1.11.34 has a CRITICAL SQL injection vuln (CVE-2026-28430, CVSS 9.3). Unauth attackers can hijack admin accounts & access PII. Upgrade to 1.11.34 ASAP. No public exploits yet. https://radar.offseq.com/threat/cve-2026-28430-cwe-89-improper-neutralization-of-s-36133b16 #OffSeq #SQLInjection #Chamilo #InfoSec
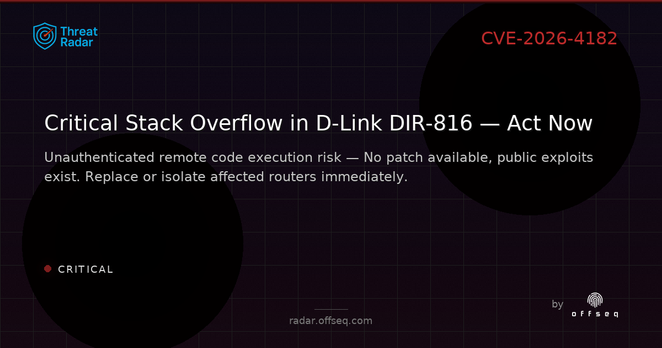
🚨 CRITICAL: CVE-2026-4182 in D-Link DIR-816 (v1.10CNB05) — stack buffer overflow in /goform/form2Wl5RepeaterStep2.cgi enables remote code execution. No patch, public exploit exists. Replace or isolate devices now! https://radar.offseq.com/threat/cve-2026-4182-stack-based-buffer-overflow-in-d-lin-4b5e9537 #OffSeq #DLink #IoTSecurity
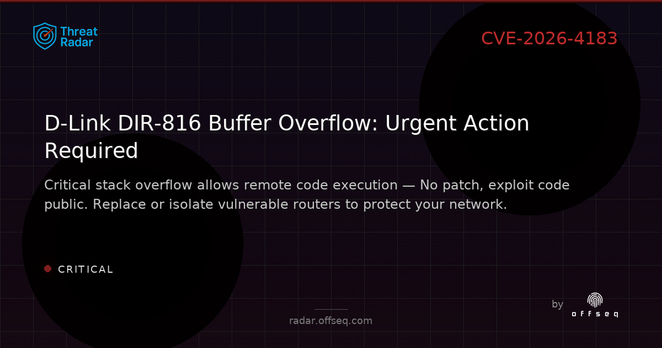
🔎 CVE-2026-4183 (CRITICAL, CVSS 9.3): D-Link DIR-816 (v1.10CNB05) stack buffer overflow via /goform/form2WlanBasicSetup.cgi. Exploit code public, no patch. Replace or isolate devices ASAP! https://radar.offseq.com/threat/cve-2026-4183-stack-based-buffer-overflow-in-d-lin-2982ced2 #OffSeq #CVE20264183 #IoTSecurity
🛡️ HIGH severity alert: CVE-2026-4255 in TR-VISION HOME (≤2.0.5) enables DLL hijacking; local attackers can escalate privileges via side-loading. Restrict write access & monitor for rogue DLLs. https://radar.offseq.com/threat/cve-2026-4255-cwe-829-inclusion-of-functionality-f-64ab002d #OffSeq #Infosec #CVE20264255 #Windows
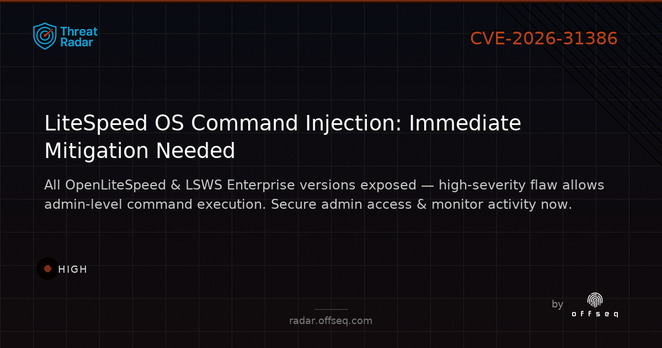
🔒 CVE-2026-31386 (HIGH): All LiteSpeed OpenLiteSpeed/LSWS Enterprise versions are vulnerable to OS command injection by admins. No exploits seen yet, but impact = full system compromise. Tighten admin controls & monitor! https://radar.offseq.com/threat/cve-2026-31386-improper-neutralization-of-special--9aa4ef0e #OffSeq #LiteSpeed #Infosec
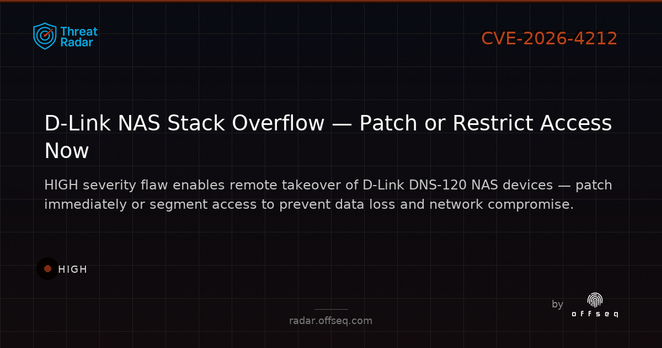
🚨 CVE-2026-4212 (HIGH, CVSS 8.7): D-Link DNS-120 NAS stack buffer overflow in /cgi-bin/download_mgr.cgi enables remote, unauthenticated compromise. Patch or restrict access now. https://radar.offseq.com/threat/cve-2026-4212-stack-based-buffer-overflow-in-d-lin-423aef88 #OffSeq #Vulnerability #DLink #BlueTeam
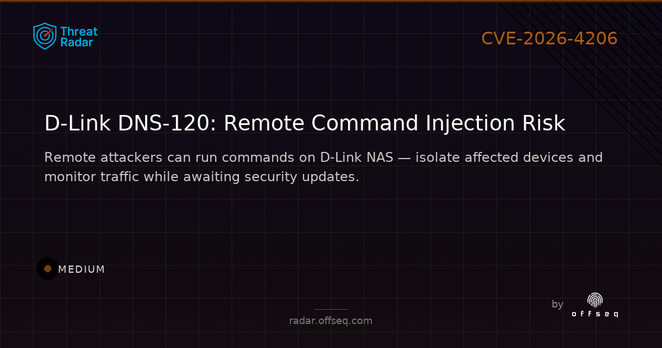
CVE-2026-4206: MEDIUM severity command injection in D-Link DNS-120 NAS (20260205). Remote, unauthenticated exploit possible — PoC public, patch ASAP or restrict access. Monitor for suspicious /cgi-bin/dsk_mgr.cgi activity. https://radar.offseq.com/threat/cve-2026-4206-command-injection-in-d-link-dns-120-65477eea #OffSeq #DLink #Vuln
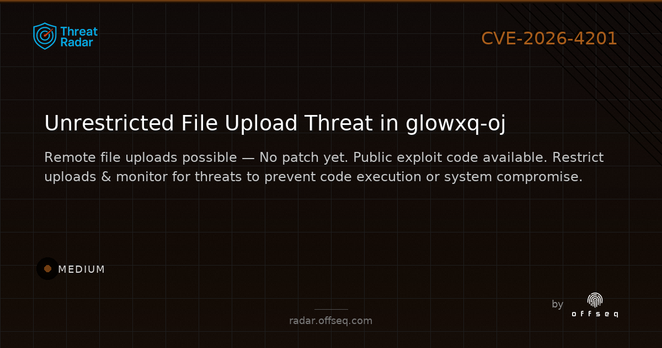
CVE-2026-4201 (MEDIUM, CVSS 6.9) in glowxq-oj allows remote, unauthenticated file uploads — risk of code execution. No patch, public exploit exists. Restrict upload access, validate files, monitor closely. https://radar.offseq.com/threat/cve-2026-4201-unrestricted-upload-in-glowxq-glowxq-224c8b75 #OffSeq #Vulnerability #CyberSecurity
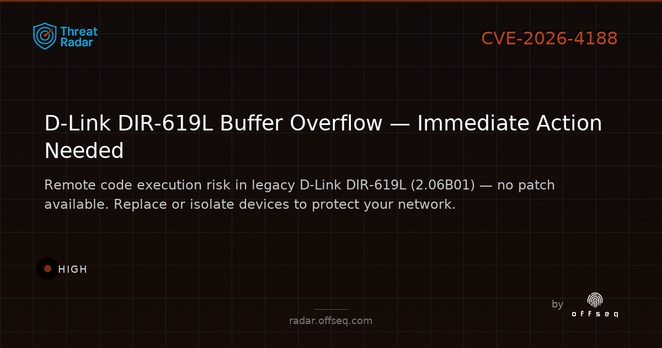
CVE-2026-4188: HIGH severity stack-based buffer overflow in D-Link DIR-619L (2.06B01). Allows remote, unauthenticated RCE. Device is unsupported — replace or strictly isolate! Exploit is public. More: https://radar.offseq.com/threat/cve-2026-4188-stack-based-buffer-overflow-in-d-lin-4643e6f2 #OffSeq #Vuln #DLink #InfoSec
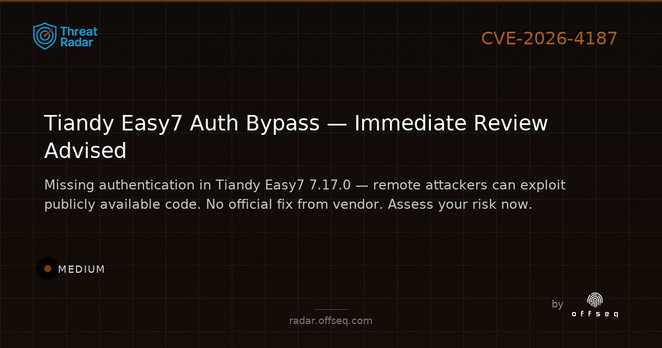
⚠️ MEDIUM severity: Tiandy Easy7 Integrated Management Platform 7.17.0 has a missing authentication bug (CVE-2026-4187) in Device Identifier Handler. Public exploit exists. No vendor fix yet — review exposure & restrict access. https://radar.offseq.com/threat/cve-2026-4187-missing-authentication-in-tiandy-eas-d0083b25 #OffSeq #Vuln #Tiandy #Cybersecurity
⚠️ CRITICAL: D-Link DIR-816 (1.10CNB05) stack-based buffer overflow via pskValue in /goform/form2Wl5BasicSetup.cgi. Exploit is public, remote code execution possible. Device is EOL — isolate or replace! CVE-2026-4184 https://radar.offseq.com/threat/cve-2026-4184-stack-based-buffer-overflow-in-d-lin-8b4d54d9 #OffSeq #DLink #Vuln
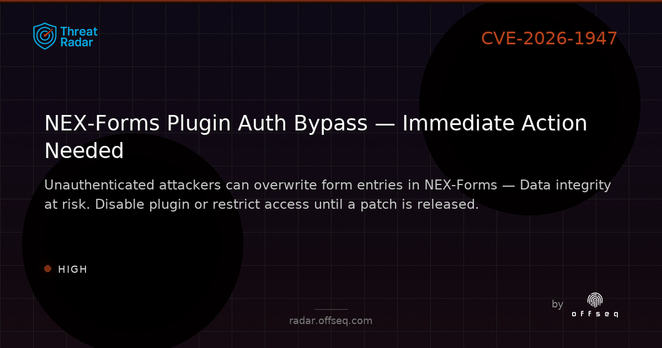
🚨 CVE-2026-1947: HIGH severity in NEX-Forms – Ultimate Forms Plugin for WordPress (all versions ≤9.1.9). Unauthenticated attackers can overwrite form entries via IDOR. Disable plugin or restrict access ASAP! https://radar.offseq.com/threat/cve-2026-1947-cwe-639-authorization-bypass-through-412339ff #OffSeq #WordPress #Vuln #InfoSec
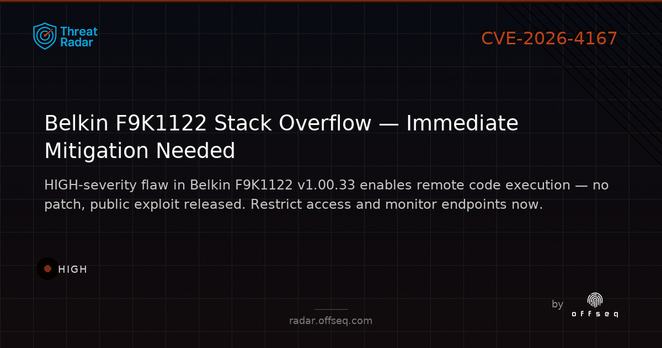
⚠️ HIGH-severity: CVE-2026-4167 stack overflow in Belkin F9K1122 v1.00.33. Remote attackers can exploit /goform/formReboot — no patch, public exploit out. Restrict access, monitor for attack attempts. https://radar.offseq.com/threat/cve-2026-4167-stack-based-buffer-overflow-in-belki-ac4818a6 #OffSeq #CVE20264167 #IoTSecurity
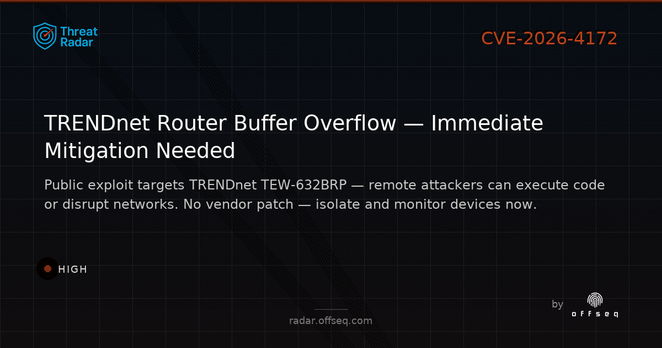
🚩 HIGH severity: CVE-2026-4172 in TRENDnet TEW-632BRP (v1.010B32) — stack-based buffer overflow in /ping_response.cgi (ping_ipaddr). Public exploit, no patch. Isolate, restrict access, and monitor now! https://radar.offseq.com/threat/cve-2026-4172-stack-based-buffer-overflow-in-trend-df028a4c #OffSeq #Infosec #RouterVuln
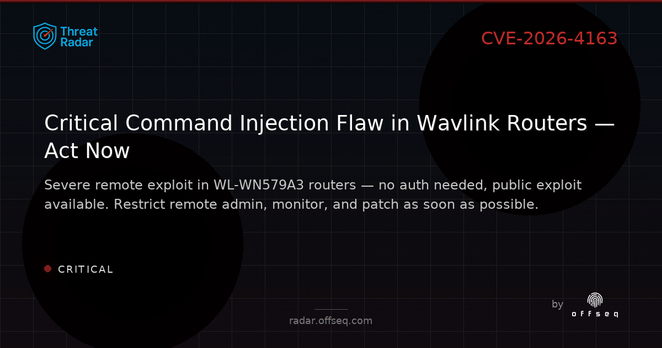
⚠️ CRITICAL: CVE-2026-4163 in Wavlink WL-WN579A3 (220323) enables remote unauthenticated command injection via /cgi-bin/wireless.cgi. Exploit is public — restrict remote admin, monitor logs, and patch ASAP. https://radar.offseq.com/threat/cve-2026-4163-command-injection-in-wavlink-wl-wn57-5fa0760b #OffSeq #Vuln #IoTSecurity
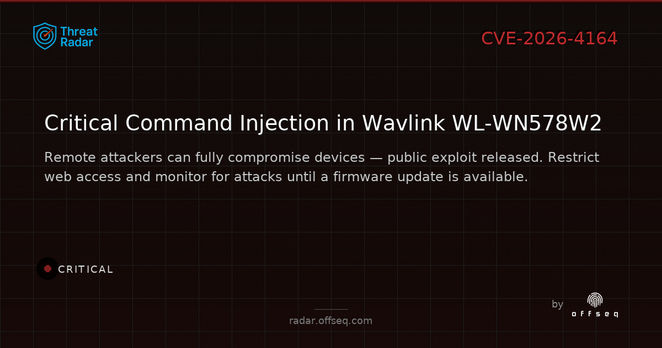
🚩 CVE-2026-4164 (CRITICAL): Wavlink WL-WN578W2 (221110) is vulnerable to remote command injection via POST to /cgi-bin/wireless.cgi. Public exploit is out. Restrict access, monitor logs, and upgrade ASAP. https://radar.offseq.com/threat/cve-2026-4164-command-injection-in-wavlink-wl-wn57-c028dcbd #OffSeq #CVE #RouterSecurity #IoTSecurity
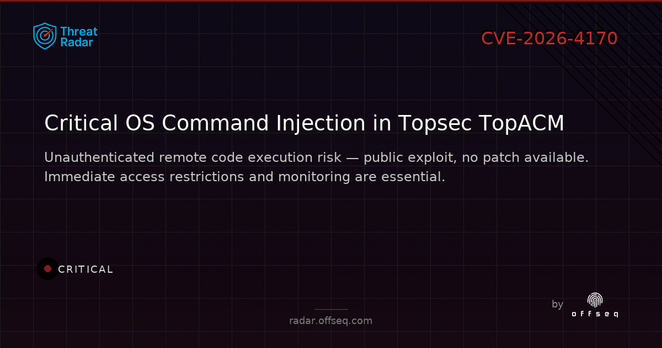
🔴 CRITICAL: CVE-2026-4170 in Topsec TopACM 3.0 enables unauthenticated OS command injection via 'template_path' in /nmc_sync.php. No patch, public exploit out. Restrict access, deploy WAF/IDS, monitor logs urgently! https://radar.offseq.com/threat/cve-2026-4170-os-command-injection-in-topsec-topac-9e1efe11 #OffSeq #vuln #cybersecurity