DNS-based staging via ClickFix represents tactical evolution.
Per Microsoft:
• Cmd.exe → nslookup execution
• Hardcoded external DNS resolver
• Payload embedded in DNS Name: response
• ZIP retrieval from azwsappdev[.]com
• Python-based reconnaissance
• VBScript persistence via Startup LNK
• ModeloRAT deployment
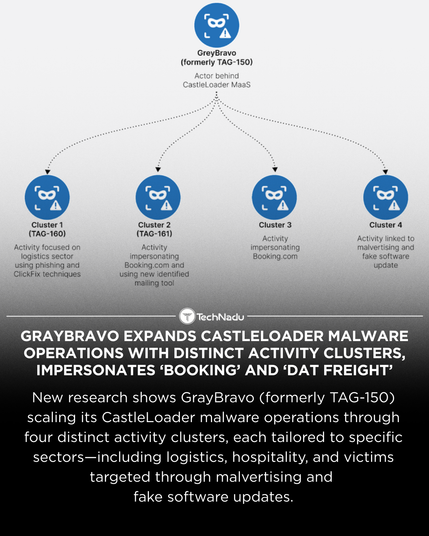
• Lumma Stealer distribution via CastleLoader (GrayBravo)
Campaign telemetry also discussed by Bitdefender and Kaspersky.
DNS offers:
• Reduced dependency on HTTP
• Traffic blending with legitimate queries
• Lightweight validation signaling
Detection priorities:
• Anomalous nslookup patterns
• External DNS resolver usage
• Suspicious Startup LNK creation
• DNS response content inspection
Is your EDR correlating DNS queries with process lineage?
Engage below.
Follow @technadu for advanced threat analysis.
#ThreatIntel #ClickFix #DNSStaging #ModeloRAT #LummaStealer #CastleLoader #DetectionEngineering #BlueTeam #SOC #Infosec #CyberOperations #MalwareAnalysis