📢 Last week, I had the pleasure of visiting the beautiful University of Delaware to speak about supply chain security, and reconnect with friends and colleagues!
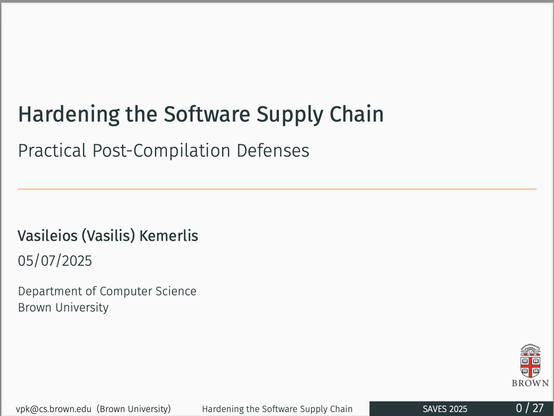
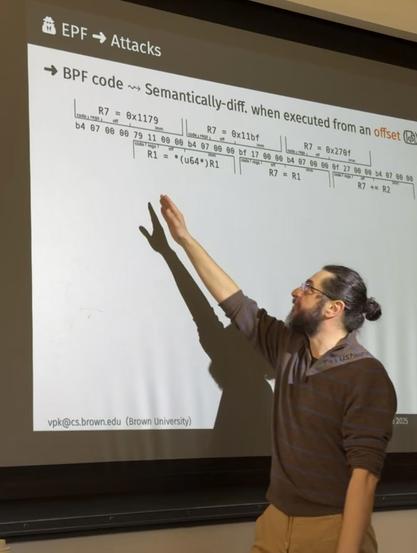
My talk, titled "Hardening the Software Supply Chain: Practical Post-Compilation Defenses", was part of the SAVES (Securing Autonomous Vehicle Ecosystems and Supply Chains) workshop at IEEE MOST (International Conference on Mobility: Operations, Services, and Technologies -- https://ieeemobility.org/MOST2025/). I discussed both the pressing open problems in this rapidly evolving field and the next-generation challenges of protecting critical infrastructure from software supply chain attacks.
I also shared a few highlights from our recent research efforts over the past five years re: supply-chain security:
✳️ BinWrap (ACM ASIACCS 2023, Distinguished Paper Award 🏆: 📄 https://cs.brown.edu/~vpk/papers/binwrap.asiaccs23.pdf, 💾 https://github.com/atlas-brown/binwrap) -- HW-assisted (via Intel MPK) sandboxing of native Node.js add-ons.
✳️ sysfilter (RAID 2020: 📄 https://cs.brown.edu/~vpk/papers/sysfilter.raid20.pdf, 💾 https://gitlab.com/brown-ssl/sysfilter) -- Automated system-call policy extraction and enforcement in binary-only applications.
✳️ Nibbler (ACSAC 2019: 📄 https://cs.brown.edu/~vpk/papers/nibbler.acsac19.pdf, 💾 https://gitlab.com/brown-ssl/libfilter) -- Shared-library code debloating.
(Joint work with Nikos Vasilakis, Sotiris Ioannidis, Georgios Portokalidis, Rodrigo Fonseca, Di Jin, Grigoris Ntousakis, George Christou, David Williams-King, Ioannis Agadakos, and Nicholas DeMarinis.)
If this area of research interests you, you might also find our recent work on Quack (hardening PHP code against deserialization attacks, NDSS 2024: 📄 https://cs.brown.edu/~vpk/papers/quack.ndss24.pdf 💾 https://github.com/columbia/quack) worth a look.
Thank you, Xing Gao and the University of Delaware CIS department for the warm welcome, thoughtful discussions, and the tour of the acclaimed CAR (https://www.thecarlab.org) lab!
#binwrap #sysfilter #nibbler #brownssl