Tutorial Hacking Servidores
https://wiki.acosadores.net/doku.php?id=tutorial:hacking-servidores
#hacking #redes #informática #fuzzing #nmap #curl #seclists #ffuf #feroxbuster #cewl #searchsploit #wpscan #metasploit #grep
#ffuf
Fell into a bit of a rabbit hole today and went from "I wonder if I still know how to use #ffuf, let's see if I can build a command to check for a specific issue I encountered recently" to submitting my first six #BugBounty reports, with another three in the pipeline once HackerOne lets me submit again (I seem to be limited to a single open report right now?).
It's also a trial balloon for me - if something comes of this, I may start refining this and building more detections. If they all get closed without a bounty or even a thank-you, I may move on to other stuff. Based on what I heard from other people, I’m not getting my hopes up, but am open to being pleasantly surprised.
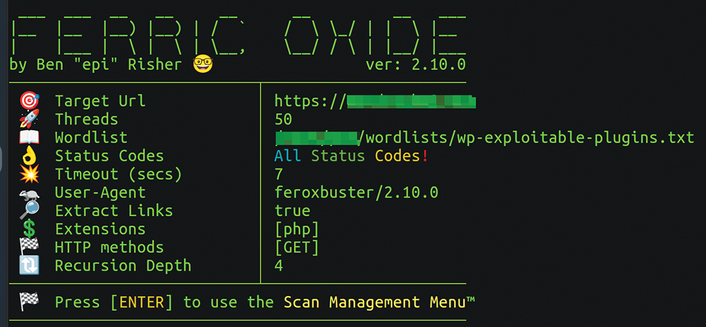
In this week's Linux Update newsletter, Chris Binnie looks at the enumeration tools feroxbuster and ffuf for automating search during a cyberattack
https://www.linux-magazine.com/Issues/2025/290/Enumerating-Resources
#security #tools #feroxbuster #ffuf #enumeration #cyberattack #automation #fuzzing
Исследование веб-приложений с помощью утилиты Ffuf
В сфере информационной безопасности и тестирования веб-приложений каждая малейшая уязвимость может привести к серьезным последствиям. Надежным помощником в обнаружении скрытых угроз и проведения глубокого анализа безопасности веб-систем может стать утилита Ffuf. Разбираемся с фаззингом с Ffuf и исследуем несколько ключевых методов его применения.
https://habr.com/ru/companies/skillfactory/articles/810293/
#безопасность_вебприложений #информационная_безопасность #фаззинг #безопасность_сайтов #фаззингтестирование #Ffuf #команды_Ffuf #защита_сайта
Intro to https://github.com/ffuf/ffuf from the author @joohoi at #helsec 5 year anniversary Meetup.
#BurpSuite - #Repeater ✅
Burp Suite - #Intruder 🔧
Intruder...auch ein geiles Teil, wobei man ja leider bei der Community Edition von Burp nur eine begrenzte Anzahl an Fragen zur Verfügung hat...aber es gibt ja dafür alternative Comandline-Tools wie #ffuf und co.
Morgen kommt dann einiges an praktischen Übungen diesbezüglich auf mich zu. Ich hoffe, ja dass ich da ganz gut alleine durchkomme. 👀 💪
[15🔥] #tryhackme
Authentication Bypass - I have just completed this room! Check it out: https://tryhackme.com/room/authenticationbypass #tryhackme #security #Auth #bypass #ffuf #enum #bruteforce #authenticationbypass via @RealTryHackMe
#infosec #hacking
Day 080 becoming a hacker!
ffuf stands for Fuzz Faster U Fool and it’s a tool written in Golang used for web enumeration, fuzzing, and directory brute forcing.
Let’s find out how ffuf works in our daily #FromZeroToHacker challenge.
#FromZeroToHacker #Hacking #hacker #ethicalhacker #ffuf
https://letslearnabout.net/hacking/from-zero-to-hero/day-080-ffuf-for-beginner/
Anyone other #infosec peeps always reading “ffuf” as “eff off”? No? Just me then 😬
If you were annoyed by the recent multi-lines output bug in #ffuf in your #pentests and #bugbounty engagements, I've just fixed it: https://github.com/ffuf/ffuf/pull/656
It's not yet merged, but in the meantime you can apply the patch locally and recompile ffuf if needed! 🤗
✨ ffuf(Fuzz Faster U Fool)
▶️Fest web fuzzer written in Go that allows typical directory discovery, virtual host discovery (without DNS records) and GET and POST parameter fuzzing
GitHub link:
https://github.com/ffuf/ffuf
▶️ Resources
👉 Comprehensive Guide on ffuf
https://www.hackingarticles.in/comprehensive-guide-on-ffuf/
👉 How to Fuzz Web Applications using FFuf – Web Security Tutorial
https://www.freecodecamp.org/news/web-security-fuzz-web-applications-using-ffuf/
👉Top 25 Example Usage of ffuf Web Fuzzer
https://allabouttesting.org/top-25-example-usage-of-ffuf-web-fuzzer/
👉 HOW TO FIND ZERO-DAY VULNERABILITIES WITH ffuf
https://www.securitynewspaper.com/2022/06/11/how-to-find-zero-day-vulnerabilities-with-fuzz-faster-u-fool-ffuf-detailed-free-fuzzing-tool-tutorial/
#infosec #ffuf #pentesting #bugbounty #bugbountytip #redteamtip #zeroday #kalilinux
Just published part 3 of my blog series on #Java #Spring Actuators - today, I'm discussing how to find exposed Actuators using dynamic testing with my favorite swiss army knife for web security tests: ffuf.
If you missed the previous articles or don't know what I am talking about: In part 1, I discuss why Spring Actuators can be dangerous if you inadvertently expose them to the internet (https://blog.maass.xyz/spring-actuator-security-part-1-stealing-secrets-using-spring-actuators), and in part 2 I show you how to use #semgrep to analyze your code for common misconfigurations related to them (https://blog.maass.xyz/spring-actuator-security-part-2-finding-actuators-using-static-code-analysis-with-semgrep). This third article rounds out the attacker side with a look at dynamic testing using #ffuf. Now, on to writing a final article from the perspective of the defender.
#ffuf - Fuzz Faster U Fool on multiple hosts
for i in cat urls.txt; do ffuf -u $i/FUZZ -w wordlist.txt -mc 200,302,401 -se ;done
Pro Tip: If you are not finding any valid endpoints, try within a discovered path adding ..;/ to the url.
ie http://site.tld/somedir/..;/FUZZ
#bypass #payloads https://github.com/aufzayed/bugbounty/blob/main/403-bypass/403_url_payloads.txt
Fuzzing & Directory Brute-Force With ffuf https://peertube.su/videos/watch/29184157-3ce9-470f-aeee-5e79d51cb957